Hidden Bottlenecks That Affect Productivity
If you run a business, you’ve probably had this thought more than once:
“Why does everything take longer than it should?”
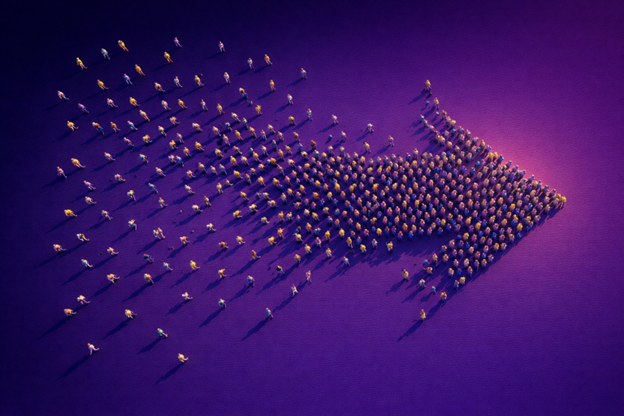
It’s usually not because your team isn’t capable or motivated. More often, it’s because everyday work is being slowed down by small points of friction built into your systems and processes—things that developed over time and were never intentionally designed.










