
Technology is an important element of modern business. Without it, most organizations wouldn’t be able to serve their clients effectively or keep their operations running smoothly. Unfortunately, though, with our increased reliance on technology, security risks are only continuing to grow each year.
However, addressing these risks effectively doesn’t necessarily mean you need to invest heavily in complicated IT solutions. While advanced security solutions certainly serve a purpose, many large-scale cyberattacks and data breaches can be avoided by simply sticking to a few good security habits.
In this blog, we’ll touch on three practical, but incredibly beneficial IT habits your business can start introducing today that will significantly reduce your digital attack surface while improving your overall cybersecurity posture.
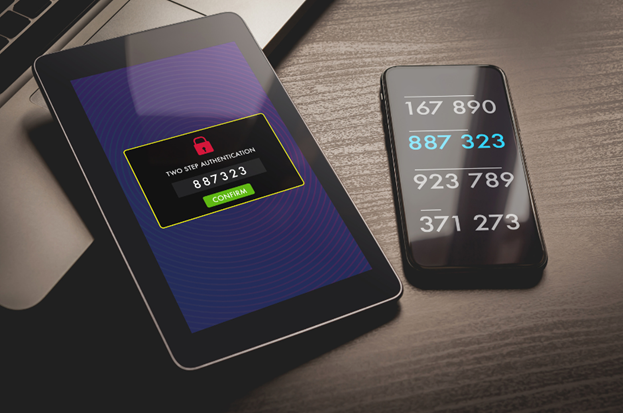
Multi-factor authentication, also known as MFA, is a protective security measure that can be applied to company systems and online platforms. MFA introduces a layered security approach to system security outside of traditional password protection. Essentially users need to provide more than one form of authentication – such as a fingerprint or randomly generated access code – before being granted access to a system.
Although passwords have always been an important part of business security, they’re often not enough to keep more experienced cybercriminals at bay. If a password is ever compromised, malicious parties can easily pose as legitimate employees when accessing sensitive business data or navigating through company networks. MFA effectively minimizes this from happening by incorporating an extra layer of security that is required before access is granted.
Even if unauthorized parties gain access to user credentials, they will still face a significant barrier, as they would need to successfully complete the additional authentication step–whether it’s a one-time code, biometric verification, or security key confirmation.
There are several different methods of adding MFA to your business. These include:
Your employees are the first line of defense when it comes to keeping your business protected from ongoing security threats. One of the fundamental best practices they can follow is establishing good password hygiene. This involves following certain strategies when it comes to creating and maintaining all business credentials across various platforms and services.
Simple, easy-to-remember passwords don’t just make it more convenient for employees to remember their login credentials – the same also applies to cybercriminals. A big part of maintaining good password hygiene is using longer, more complex password combinations – making use of capital and lowercase letters, numbers, and special characters. It’s also essential to never use the same username/password combination for more than one login.
Remembering login credentials for a wide range of applications and services isn’t easy for many employees. This is why many choose to use more memorable but weaker passwords. Using a commercial password manager is a much safer and more effective method for enforcing good password hygiene.
Password managers use a heavily encrypted “digital vault” where all employee logins are stored. These tools make it much easier to create complicated passwords that are hard to remember but can automatically be used by employees when logging in to various accounts. This not only simplifies password management for everyone but also helps the business implement supporting best practices such as changing passwords every few months to strengthen company logins further.

One of the most important things to realize as a growing business is that cybersecurity isn’t just your IT department’s responsibility. Everyone in the business – from senior management to IT, sales, customer services, and finance – plays an important role in keeping the business more secure.
Implementing various cybersecurity training initiatives is an effective way to instill this importance in all employees. Taking this approach helps to build important awareness concerning emerging business threats, how to properly identify them, and the necessary steps required to mitigate any ongoing risks associated with them.
To get the most out of your cyber training initiatives, below are some strategies you can put in place:
While MFA, strong passwords, and training are all crucial, there are some other essential practices you can follow to significantly improve your IT security.
Regular system and database backups act as an insurance policy for data loss in the event of a hardware problem, ransomware attack, or accidental deletion. However, simply having backups isn’t enough–it’s crucial to regularly test and verify that your backups work as expected. Periodic restoration tests ensure that data can be successfully recovered when needed, minimizing downtime and preventing unpleasant surprises during a crisis.
Equally important to backups is to ensure all your programs and company software stays up to date. Outdated software can be easily exploited by cyber attackers who find gaps in platform security or modifiable registries. However, keeping your software ensures you’re downloading and updating important security patches designed to fill these gaps before cybercriminals can leverage them. While they may not seem that important, regular software and hardware updates are another easy, but impactful way to strengthen your security.
Tackling cybersecurity for your business doesn’t need to be an intimidating process. By implementing a variety of practical, but effective IT habits, you’ll significantly lower your organization’s risk profile while continuing to strengthen your security protocols.
LDD Consulting is a trusted IT partner that specializes in helping growing businesses establish the foundational security elements they need to protect themselves against emerging cyberthreats. With over 20 years of experience in IT management, we specialize in building resilient security strategies that support your business’ growth–without compromising protection.
Don’t wait until a cyber incident disrupts your operations. Schedule a free consultation with LDD Consulting today and let’s assess your security needs before threats become costly problems.